Building ITAM Foundations: A Quick Guide to Inventory and Discovery
This article provides a quick introduction to the concepts of inventory and discovery, two fundamentals that sit at the heart of effective IT Asset Management (ITAM).
I’ll also be maintaining a list of tools that support inventory and discovery (from dedicated discovery technologies through to ITSM and ITAM platforms – see the bottom of this article). If I’ve missed any technology you rely on, please shout.
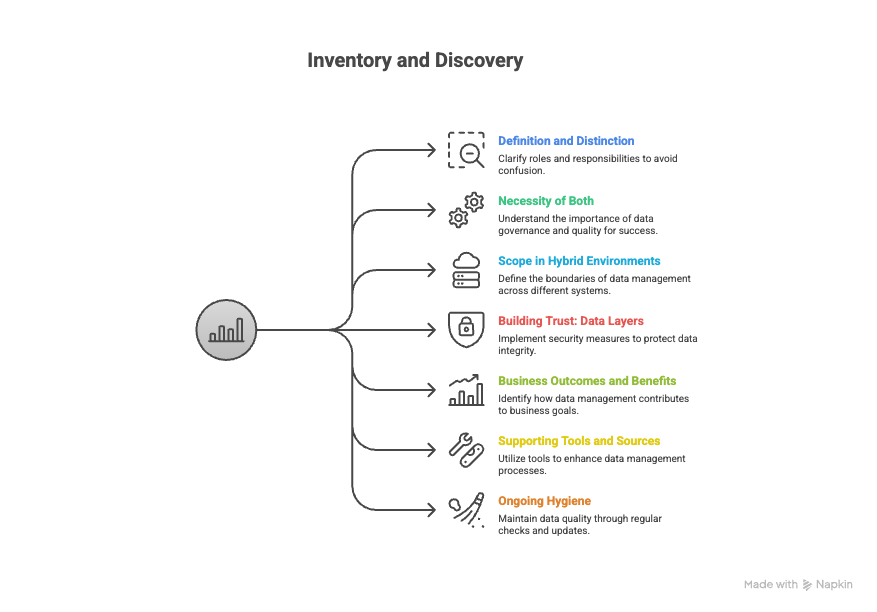
What is Inventory and Discovery?
Within the ITAM world, the terms “discovery” and “inventory” often get bundled together, almost as if they’re the same thing. They’re related and usually go hand in hand, but they are different.
To make things more confusing, other disciplines interpret these terms differently. For example, FinOps teams may talk about “inventory” and “discovery” in ways that don’t quite align with how ITAM uses them.
So it’s worth being explicit about what we mean in an ITAM context, because these concepts underpin almost everything we do.
Inventory and Discovery
What Do We Mean by “Discovery”?
From an ITAM perspective, discovery is the identification of asset existence.
Think of it as: “Doing a sweep to find out what’s really there.”
- Discovery answers questions like: What devices are actually connected to our network?
- What software is really installed, not just what we think is deployed?
- Which cloud instances and subscriptions have sprung up in our environment?
Discovery helps you move from assumptions (“we think we have 10 devices”) to facts (“we actually have 15 devices, because we ran discovery”).
It’s primarily about coverage and completeness:
Have we caught everything in our environment that we might want to track?
What Do We Mean by “Inventory”?
Inventory begins once you start tracking assets over time.
If discovery says, “This asset exists,” then inventory says: “We’re now tracking this asset, its configuration, and how it changes over time.”
Inventory covers things like:
- The configuration of a device (hardware specs, OS, installed software)
- Changes to a server (memory upgrades, role changes, repurposing)
- Software being added or removed on endpoints
- Subscriptions being upgraded, downgraded, reassigned, or cancelled
- Cloud instances being spun up, resized, reconfigured, or decommissioned
Where discovery is about finding, inventory is about maintaining an accurate, up-to-date record.
So, at a very high level:
- Discovery: Have we found everything?
- Inventory: For what we’ve found, is the data accurate and current?
Those two pillars are key to building trustworthy data.
Why You Can’t Do Just One
You can’t get away with doing only one of these and expect good outcomes.
If you only do discovery…
- You get a point-in-time snapshot of what exists. That might be useful for a quick reconciliation or an audit response, but:
You won’t see how things are changing - You can’t reliably support ongoing processes (e.g. licence optimisation, security investigations, or lifecycle management)
- You’ll constantly be surprised by changes that weren’t captured
If you only do inventory…
- You’re making a big assumption: “We know what we’ve got, and it’s complete.”
- Without proper discovery, that’s risky. You might be: Missing devices that never made it onto your register
- Blind to shadow IT, SaaS sprawl, and rogue cloud usage
- Relying on deployment data or configuration databases that are incomplete or outdated
In other words, discovery gives you confidence you’ve caught everything; inventory gives you confidence what you’ve caught is correct and current. You need both.
From Network Scans to Hybrid Reality
Historically, discovery and inventory started in traditional networked environments:
- Scanning IP ranges to find laptops, desktops, and servers
- Identifying what’s online and collecting basic device information
That world still exists, but environments are now far more complicated. Today, discovery and inventory often have to span:
- On-premise devices and data centres
- Hybrid data centres and colocation
- Multiple cloud providers and regions
- SaaS applications and user-owned subscriptions
- User domains and identities
- Containers, microservices, and ephemeral workloads
The job hasn’t gone away, it’s just become more fragmented and dynamic. The core questions, however, remain the same:
What do we have? (discovery)
What state is it in, and how is it changing? (inventory)
Enterprise Inventory is an aggregate of sources
Inventory and discovery data very rarely live in one neat tool, it’s scattered across everything you already own. Good tools recognise this and become aggregators of data sources.
Cloud consoles act like CMDBs for IaaS and PaaS. FinOps and cloud governance tools sweep accounts and tie resources back to tags, owners and cost. Network and IPAM tools quietly spot anything with an IP address. DEX tools show what’s really running on laptops. SaaS discovery, hypervisor and Kubernetes platforms know about SaaS apps, VMs and containers that never touch your CMDB. DCIM, backup and DR systems see the physical kit and protected workloads. Identity platforms give you the people view. OT/IoT and SBOM tools surface industrial kit and software components. The ITAM job is to plug into these feeds and join them up into something trustworthy, rather than pretending one magic tool will do it all.
Layers of Data to build Trust
When you’re collecting inventory and discovery data, it helps to think in terms of three layers: where you trust, where you find, and where you enrich.
- First, define an authoritative system of record (SoR), usually your ITAM platform and/or CMDB, which is the place you trust first and reconcile everything back to.
- Then consider your discovery feeders: the tools that tell you what actually exists in your estate by scanning infrastructure, endpoints, cloud, SaaS, networks, and so on.
- Finally, plug in enrichment sources that add context to those raw records, cost, risk, usage, ownership, and relationships, so that the data in your SoR isn’t just technically accurate, but also meaningful for decisions across IT, finance, risk, and procurement.
See also:
Triangulate for Accuracy, and Is 95% accuracy good enough for ITAM?.
Who Uses This Data?
Once we’ve collected discovery and inventory data, many different teams can make use of it. ITAM isn’t the only consumer.
Cost efficiency and audit-ready compliance
Optimising licences, avoiding waste, staying compliant, managing vendor audits, handling renewals, and rationalising software portfolios all depend on accurate discovery and inventory.
Reduced security risk and faster incident response
You can’t secure what you don’t know you have. Vulnerability management, patching, incident response, and asset-based risk assessments all rely on trustworthy inventory.
Higher service availability and smoother change
If you’re logging an incident, you need to know which asset it relates to. CMDB records, CI relationships, and change management all hinge on inventory quality.
Cloud and SaaS cost optimisation with clear accountability
For cloud and SaaS, understanding what’s in use, who owns it, and how it’s configured feeds directly into cost optimisation and accountable spend.
Improved sustainability metrics and ESG reporting
Quantifying and reducing environmental impact (e-waste, energy use, embodied carbon, etc.) starts with knowing what you have, where it is, and how long it lives.
Ultimately, ITAM’s reputation, and the reputation of the ITAM team, lives or dies on the trust people place in our data. Discovery and inventory are the foundations of that trust.
Types of Tools and Data Sources
There are several approaches and tool categories that can support discovery and inventory.
Dedicated Discovery & Inventory Tools
These are tools whose primary focus is inventory and discovery. They specialise in:
- Scanning networks and environments
- Identifying devices, software, and services
Aggregating data sources and enriching to reach the truth - Normalising and structuring asset data
They often serve as a core feed into ITAM, security, and ITSM platforms.
Dedicated Discovery and Inventory Tools are “best of breed” in comparison to the suite approach of ITAM and ITSM platforms (see below), the trouble with the justification of best of breed tools is justifying their investment when other “good enough” data sources exist. So it becomes less about a business case for inventory and discovery, but building the business case for better inventory and discovery.
IT Service Management (ITSM) Platforms
Many ITSM platforms now include a discovery and CMDB component because they:
- Need a record of assets (CIs) to underpin incidents, problems, and changes
- Need accurate configuration data for impact analysis and service mapping
While their primary mission is service management, they can be powerful sources of inventory and discovery data for ITAM when implemented well.
ITAM / SAM / Licence Management Tools
ITAM and SAM tools depend on good data feeds – including discovery and inventory – in order to:
- Calculate consumption
- Model licence positions
- Enable optimisation and forecasting
Some tools include their own discovery capabilities; others integrate with third-party discovery tools, ITSM platforms, or deployment systems.
“Other” Data Sources, and the “Muddle Through” Approach
Beyond formal tools, organisations often rely on:
- Software deployment and patching systems
- Configuration management tools
- Cloud provider consoles and APIs
- SaaS admin consoles
- Spreadsheets and ad-hoc reports
These can be stitched together to build a picture of the environment. It’s not always elegant or 100% accurate, but many organisations “muddle through” with this approach, especially when budgets are tight or tools are fragmented. Common tools / data sources include things like Microsoft Intune, Microsoft Configuration Manager (SCCM), VMware Workspace ONE, Jamf Pro, and Ivanti Endpoint Manager.
The key is to be honest about the limitations of these sources and to design ITAM processes that account for gaps and inaccuracies.
Start with the Business Outcome
Strictly speaking, it’s beyond the scope of this quick introduction to design a full-blown discovery and inventory strategy. But it’s worth calling out one crucial point: Always start with the business outcome you’re trying to support.
Ask questions like:
- What is the business focused on right now?
- Which outcomes can ITAM support (e.g. cost savings, risk reduction, audit readiness, sustainability, agility)?
- What evidence do we need to demonstrate impact and build trust?
From there, work backwards: Define the decisions and processes you want to support (e.g. cloud cost optimisation, audit defence, hardware lifecycle planning).
Identify the data required to support those decisions.
Work out what needs discovery (have we found everything relevant?) and what needs ongoing inventory (is it accurate and up to date?).
Select or refine tools and data sources accordingly.
At a high level:
- Discovery answers: Have we caught everything that matters?
- Inventory answers: Is the data we have accurate and current enough to be trusted?
Get those two pillars right, and you’re in a strong position to layer on licensing rules, cost models, risk frameworks, and everything else that makes ITAM valuable.
The alternative, and a common failing with all things ITAM, is to try and collect data for everything, because we can, and shudder to a halt because you’ve tried to boil the ocean.
Keeping it alive
Inventory and discovery is not a “set it and forget it” exercise; no matter how slick the sales presentation from your tool manufacturer, the real-life hygiene of your discovery and inventory system might include checking scheduled scans actually ran and fixing failed agents or credentials, updating discovery scopes when new networks, cloud accounts or SaaS tenants appear, clearing down “unknown” or duplicate records, dealing with stale “last seen 90 days ago” devices, and reconciling what the tools say with HR, finance and what the service desk sees on the ground.
Summary: Don’t Skimp on the Foundations
Inventory and discovery can be seen as “back-office plumbing” , not as glamorous as AI or the latest tech, but absolutely essential.
From an ITAM perspective, they are:
- Fundamental to trustworthy data
- Critical for information security, cost control, and risk reduction
- Enablers for better agility and decision-making
- Foundations for sustainability reporting and environmental impact reduction
In short: a lot of good things in ITAM stem from getting inventory and discovery correct and accurate in the first place. It really shouldn’t be overlooked.
DISCOVERY AND INVENTORY TOOLS
Dedicated discovery & inventory tools
- Belarc – Belmanage
- Device42 – Discovery & CMDB (Freshworks)
- HCL BigFix – BigFix Inventory
- JDisc
- Lansweeper – Technology Asset Intelligence Platform
- Raynet – RayVentory / Raynet One IT Asset Discovery & Inventory
- xAssets – Network Discovery & IT Asset Management
ITAM & SAM platforms
- Certero – Certero for Enterprise ITAM
- Eracent – ITMC Discovery & IT Management Center
- EZO – Asset Sonar
- Flexera – Flexera One IT Asset Management & IT Asset Discovery
- HCL – Z Asset Optimizer (Mainframe)
- Infraon – Infraon Assets
- InvGate – InvGate Asset Management & IT Asset Discovery
- Ivanti – Neurons for Discovery & Ivanti ITAM
- License Dashboard – SAM Platform
- ManageEngine – AssetExplorer
- Matrix42 – IT Asset Management / Software Asset Management
- Oomnitza – Enterprise Technology Management
- ServiceNow – IT Asset Management + ServiceNow Discovery
- USU – IT Asset Management / IT Asset Inventory
ITSM & CMDB platforms
- Alloy Software – Alloy Discovery / AlloyScan + Alloy Navigator
- Atlassian – Jira Service Management + Assets / Assets Discovery
- BMC – BMC Helix ITSM + BMC Helix Discovery
- Freshworks – Freshservice (Discovery & CMDB)
- GLPI – GLPI ITSM
- ManageEngine / Zoho – ServiceDesk Plus
- OpenText – Universal Discovery & CMDB
- SolarWinds – SolarWinds Service Desk + SolarWinds Discovery
- SysAid – ITSM with Asset Management & Network Discovery
Endpoint management, RMM & DEX
- 1E
- Atera – RMM/PSA
- Auvik – Network Management & Discovery
- IT Glue – Documentation & Asset Management (Network Glue)
- N-able – N-central
- Nexthink – Digital Employee Experience Platform
- NinjaOne – RMM & Endpoint Management
- RapidFire Tools – Network Detective Pro
- Spiceworks – Spiceworks Inventory
- Tanium – Asset Discovery & Inventory
Security / vulnerability / external attack-surface discovery
Open-source & DIY ITAM / CMDB / discovery
- CMDBuild – Open-source CMDB & Asset Management
- FusionInventory – Agent & Network Discovery
- NocoBase – Low-code Backend Platform
- OCS Inventory NG
- OpenAudit
- Ralph – Asset Management / DCIM & Inventory
- Snipe-IT – Open Source IT Asset Management
- Tracmor – Cloud Asset & Inventory Tracking
- Zabbix – Monitoring with Network Discovery & Host Inventory
Workplace, facilities & lifecycle-focused asset tools
- Asset Panda – IT Asset & Inventory Management
- AssetTiger – Cloud Asset Management
- OfficeSpace – OfficeSpace Assets
- Workwize – IT Hardware Asset Management for Remote Teams
If there are any tools or data sources missing from this please shout.
Can’t find what you’re looking for?
More from ITAM News & Analysis
-
Stop Shadow IT Before It Hurts Your Business
Shadow IT often spreads quietly and quickly becomes a serious risk. Just look at the UK-based supermarket chain Co-op. A little-known remote maintenance tool used by an external IT provider was compromised. The result? Nearly 800 ... -
Why ITAM Forum Should Join the Linux Foundation: My Rationale and Your Questions Answered
TLDR. ITAM Forum has the opportunity to join the Linux Foundation as a stand-alone, self-funded project. This article covers a) What’s happening b) Why I think it’s a great move for the ITAM Forum and c) ... -
Microsoft Pricing Changes: EA Customers Face Price Increases
From 1st November 2025, Microsoft will remove all tiered pricing for Online Services under the Enterprise Agreement. This means all customers renewing or purchasing new Online Services after this date, will receive standard level A pricing ...
