ITAM is an investment in cybersecurity, not a cost
In the following article, Rishi Simbudyal from Teqtivity explains why ITAM is so critical to cyber security, and why cybersecurity professionals need ITAM more than ever.
According to IBM’s Cost of a Data Breach Report, the average impact of a data breach on organisations is $4.45 million in 2023; a 15% increase over 3 years.
The cybersecurity landscape is a battlefield. Organizations constantly deploy firewalls, train employees, and stay vigilant against the latest hacking tactics. Yet, many overlook a fundamental building block for robust cybersecurity: IT Asset Management (ITAM).
Traditionally viewed as a simple inventory tool, ITAM goes beyond cataloging hardware and software. It’s a strategic practice that provides a comprehensive view of your entire IT ecosystem, including devices, applications, licenses, and configurations. This holistic understanding empowers organisations to significantly improve their cybersecurity posture and risk management in several ways.
Why Cybersecurity Needs ITAM More Than Ever Now:
1. Aligning with Regulatory Landscape
The importance of ITAM is further underscored by recent regulatory changes. In July 2023, the Securities and Exchange Commission (SEC) adopted new rules mandating public companies to disclose material cybersecurity incidents and maintain a strong cybersecurity risk management program.
A recent report by S&P Global Ratings highlights ITAM’s impact on an organisation’s creditworthiness —the S&P report warns that neglecting ITAM as part of cyber risk management practices can negatively affect an S&P Global credit rating. S&P credit analyst Paul Alvarez said, “ITAM is foundational to effective cyber security. Its absence at an organization can be indicative of flawed cyber risk management and could weigh on our view of an entity’s creditworthiness.“
In other words, robust ITAM goes beyond safeguarding your data; it’s a financial imperative in today’s threat landscape.
2. The Insecurity of an Unmanaged IT Landscape
Imagine an IT environment lacking ITAM as a city with poorly maintained areas. In such an environment, forgotten devices, unpatched software on outdated machines, or unauthorized applications can reside undetected, creating potential security risks. ITAM acts as a responsible city planner, meticulously documenting every IT asset and its role within the network. This organized IT landscape, with all its documented assets, makes it significantly harder for attackers to find vulnerabilities and exploit them.
3. The Unexpected Security Benefit of License Compliance
Software licenses often dictate security protocols and access controls. Poor ITAM can lead to unknowingly using unlicensed software, which may have known security vulnerabilities or lack critical security updates. Conversely, strong ITAM ensures compliance with software licenses, keeping your systems up-to-date with the latest security patches and functionalities.
4. The Future of Security is Asset-Aware
The benefits of ITAM extend beyond immediate security improvements. It fosters a culture of accountability within organizations as asset ownership and responsibility become clear. Additionally, ITAM lays the groundwork for automated security measures. By integrating with EDR tools, organizations can achieve a proactive security posture, automatically identifying and addressing risks before they become exploited.
5. The Increasing Importance: A World of Connected Devices
The growing number of connected devices – laptops, smartphones, Internet of Things (IoT) devices – further amplifies the need for robust ITAM. These endpoints can easily become entry points for attackers if left unmanaged. A comprehensive ITAM strategy ensures all devices are identified, tracked, and secured, closing potential security gaps in the ever-expanding digital landscape.
Plugging the Leaks: ITAM for a Tight Ship
Beyond just identifying devices, ITAM tackles critical security concerns that stem from a lack of asset awareness:
- Lost Track of Assets? Lost Control of Security: Imagine an employee leaving the company, but their laptop remains unaccounted for. Without ITAM, you’re left guessing which device is missing, hindering your ability to take action (remote wipe, disable access) and potentially exposing sensitive data. A detailed ITAM system ensures clear asset assignment, allowing for immediate identification and lockdown of missing devices.
- Unpatched Endpoints: An Open Invitation for Attackers: Not knowing which laptops have which software versions creates a vulnerability nightmare for IT teams. ITAM integrations with EDR (Endpoint Detection and Response) tools provide real-time insights into laptop vulnerabilities. This allows IT to prioritize patching efforts, focusing on the devices most susceptible to attack.
- Offboarding with Security in Mind: Employee departures require secure asset return. Without proper ITAM, it’s difficult to track company-issued devices, potentially leaving sensitive information on unreturned hardware. A robust ITAM system streamlines the offboarding process, ensuring all assets are retrieved and company data remains secure.
- ITAM-MDM Integration: A Security Force Multiplier: ITAM’s power increases with Mobile Device Management (MDM) integration. This duo provides a unified view of mobile devices, enabling real-time discrepancy reporting. ITAM-MDM flags potential risks, like unauthorized access or unmanaged devices.
Teqtivity’s solutions bridge the gap between security and IT teams. Various integrations provide a shared view of assets, enabling faster vulnerability patching and streamlined security processes. Automated ITAM tasks free up IT personnel for strategic security initiatives, while data-driven insights from Teqtivity’s ITAM empower security teams to proactively address security risks.
Conclusion: ITAM is an Investment, not a cost
Investing in ITAM is not just about managing assets; it’s about securing your future. By providing a comprehensive view of your IT landscape, ITAM empowers organizations to proactively manage security risks, prioritize patching efforts, and ensure license compliance. In today’s threat landscape, a robust ITAM strategy is no longer optional – it’s the cornerstone of a secure digital enterprise and increasingly important for regulatory compliance.
Can’t find what you’re looking for?
More from ITAM News & Analysis
-
Stop Shadow IT Before It Hurts Your Business
Shadow IT often spreads quietly and quickly becomes a serious risk. Just look at the UK-based supermarket chain Co-op. A little-known remote maintenance tool used by an external IT provider was compromised. The result? Nearly 800 ... -
Why ITAM Forum Should Join the Linux Foundation: My Rationale and Your Questions Answered
TLDR. ITAM Forum has the opportunity to join the Linux Foundation as a stand-alone, self-funded project. This article covers a) What’s happening b) Why I think it’s a great move for the ITAM Forum and c) ... -
Microsoft Pricing Changes: EA Customers Face Price Increases
From 1st November 2025, Microsoft will remove all tiered pricing for Online Services under the Enterprise Agreement. This means all customers renewing or purchasing new Online Services after this date, will receive standard level A pricing ...
Software Licensing Training
Similar Posts
-
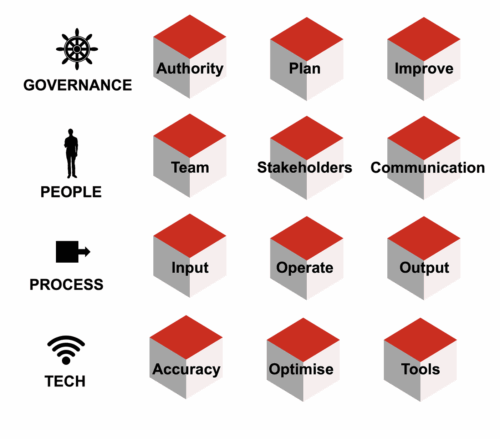
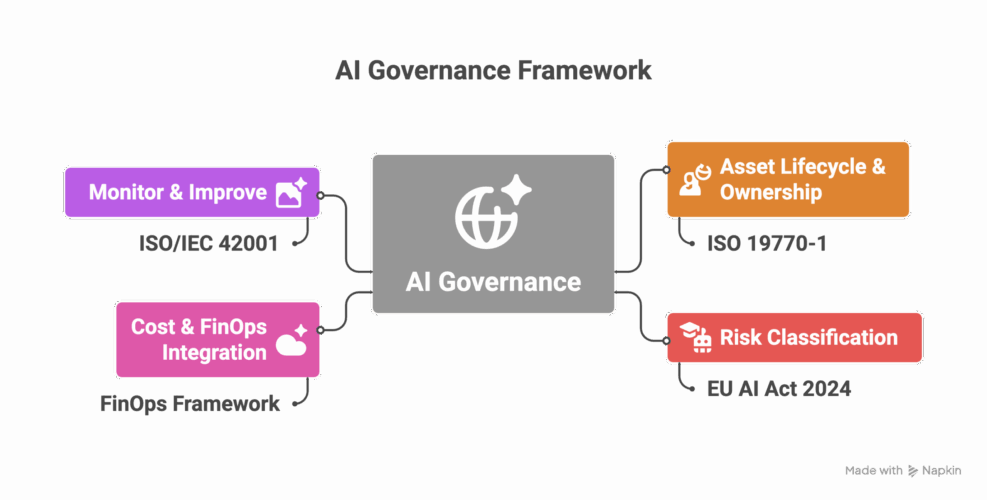
Eight steps towards AI governance
I delivered our “Managing AI as an Asset” training course the day before the Wisdom conference last week. Thank you to those who attended and provided feedback. It will be available on the LISA platform before ... -
Crawl, Walk, Run applied to ITAM Best Practice (Practical ITAM)
Since the ITAM Forum has been working in strategic partnership with the FinOps Foundation, I’ve come to admire the Crawl, Walk, Run approach to best practices, as it allows improvements and recommendations to meet the organisation ... -
Stop Shadow IT Before It Hurts Your Business
Shadow IT often spreads quietly and quickly becomes a serious risk. Just look at the UK-based supermarket chain Co-op. A little-known remote maintenance tool used by an external IT provider was compromised. The result? Nearly 800 ... -
AI Governance Through an ITAM Lens: Treat AI as a Status Change, Not a New Asset
Managing AI in the enterprise is a team sport. In this article, I want to explore specifically what ITAM brings to the table as we enter the AI era. As I’ve mentioned in previous articles on ...