Since the ITAM Forum has been working in strategic partnership with the FinOps Foundation, I’ve come to admire the Crawl, Walk, Run approach to best practices, as it allows improvements and recommendations to meet the organisation where it is in its maturity.
“A “Crawl, Walk, Run” approach to performing FinOps enables organizations to start small, and grow in scale, scope, and complexity as business value warrants maturing a functional activity. Taking quick action at a small scale and limited scope allows FinOps teams to assess the outcomes of their actions, and to gain insights into the value of taking further action in a larger, faster, or more granular way.” ~ FinOps Maturity Model
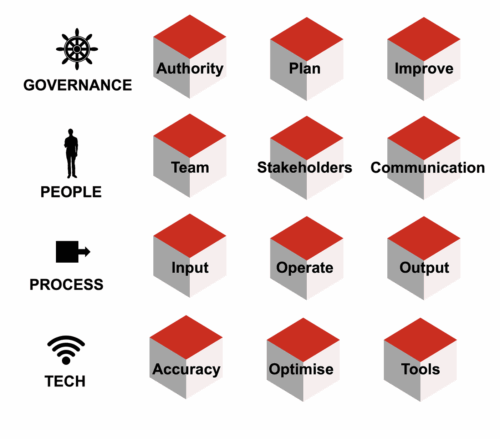
In light of this, I’ve borrowed the methodology and applied it to the 12 competency areas of the Practical ITAM framework. You can see a first draft below.
I’m working on a new version of the Practical ITAM book, and the goal is to break the achievement of these 12 competencies into the crawl, walk, and run stages, with run being conformance against ISO/IEC 19770-1.
The goal with the Practical ITAM framework was always to take the complex and sometimes overwhelming subject of ITAM and break it into manageable chunks so that ITAM professionals could prioritise, make progress and make a difference. The new edition of the book will take this a step further.
I also wish to describe the business outcomes of achieving each stage and the potential impact. If you have any suggestions on these stages or the next edition of the book, please shout. ~ thanks, Martin
Crawl, Walk, Run applied to ITAM Best Practice (Practical ITAM)
| Practical ITAM Area | Crawl (begin delivering value) | Walk (maturity & control) | Run (ISO/IEC 19770-1 conformance) |
|---|---|---|---|
| Authority | Senior management team is aware of ITAM activity and key principles. ITAM plan is supported by an ongoing communications plan tailored to audiences. | Senior management advocate sponsors, promotes, and supports ITAM activity. Key ITAM performance indicators are regularly reported to senior management. | Regular action is taken to improve the ITAM practice based on plans and metrics. |
| Plan | ITAM business plan is agreed and signed off by the business. Key risks are identified, prioritised, and managed. | Key metrics and milestones are agreed, monitored, and reviewed regularly. Business plan is regularly reviewed and modified to reflect progress. | Savings, risks averted, and ROI are measured, reported, and communicated. |
| Improve | ITAM team reports on business-aligned KPIs. Exceptions, policy breaches, and key risks are acted upon or escalated. | Reports are reviewed and agreed by the senior management team. Reports are reviewed and agreed by stakeholders. Regular stakeholder meetings with minutes, responsibilities, and actions. | Reports, reviews, and meetings operate as a documented continual-improvement cycle with evidence of actions and outcomes. |
| Team | ITAM team capabilities are regularly assessed against business plan needs. A RACI is maintained for delivery of ITAM services and objectives. | Teams have skills to track, audit, and recognise technology consumption. Teams have skills to track, interpret, and reconcile entitlement. Teams have expertise to assess risk, identify trends, and brief senior management. | Team competencies and responsibilities are evidenced via training/competency records and audit-readiness artefacts. |
| Stakeholders | Lifecycle stakeholders are identified and engaged. Verified ITAM data is used beyond ITAM (Procurement, ITSM, Security, Finance, etc.). | Stakeholders are actively involved in progress reporting and meetings. Stakeholders actively help drive ITAM improvements. Stakeholders communicate and educate the benefits of ITAM. | Cross-functional use of ITAM data and roles/responsibilities are formalised in governance with documented evidence. |
| Communication | Audience types are identified and categorised. Communication uses multiple channels flexibly. | Communications strategy meets differing audience needs. Communication effectiveness is assessed via KPIs and metrics. Communications plan evolves as the business plan evolves. | Communications operate as a managed programme with measurable outcomes, reviews, and retained records. |
| Input | Request process for new assets is automated for speed and ITAM objectives. Leaders and customers are made aware of true asset costs. | Asset catalogue/preferred list/menu reduces diversity and speeds requests. ITAM partners with Procurement on major contracts before commitments. Controls ensure assets have correct entitlement and measurement prior to deployment. | Preventative controls for request, procurement, and pre-deployment are fully embedded, monitored, and auditable. |
| Operate | ITAM is fully aware of changes via change management. ITAM collaborates with Service Desk/IT on IMAC processes to refine changes. | ITAM is fully aware of strategic IT projects (EA, PMO, Dev). Requests for users/devices/systems/services are proactively monitored and managed. | Controlled, auditable operations integrated across change, projects, and procurement: preventive checks pre-deployment/purchase, segregation of duties, SLAs/SLOs, monthly multi-function reviews, and formal ITAM sign-off for major commitments with evidence retained. |
| Output | Agreed IT use and environmental policies support lifecycle behaviours and processes. Unused software and hardware are proactively reclaimed. | Usage is tracked to determine frequency of software and device use. Asset stock levels are maintained to maximise availability and minimise costs. | Closed-loop utilisation, reclamation, and end-of-life with verifiable outcomes: automated reclamation thresholds with audit trail, managed stock targets, quarterly benefit realisation, and fully compliant EOL (chain of custody, data sanitisation certificates, environmental compliance, supplier assurances). |
| Accuracy | Auto-discovery captures devices/subscriptions/systems/users missed by inventory. Inventory of relevant devices is collected regularly to an agreed tolerance. | Inventory exceptions (new, AWOL, failed audit) are proactively managed and resolved. Software recognition and data cleansing meet an agreed tolerance. | Trustworthy, decision-grade data beyond audits: documented lineage, enforced tolerances and reconciliation rules, SLA-driven exception handling, change logging/peer review, and periodic assurance tests proving reliability for finance, security, procurement, and engineering. |
| Optimise | Contracts, maintenance, and subscriptions are managed via a renewals calendar. Exceptions, errors, or rogue purchases are recorded, acted upon, or escalated. | Management reports are maintained for high-priority suppliers. Supplier license statements and consumption reports are reviewed for accuracy. | Knowledge of licensing rules and product use rights for key publishers is actively maintained and change-tracked, with reconciliations and governance ensuring sustained optimisation. |
| Tools | An ITAM data strategy is maintained to support the business plan. Data quality is measured and verified. | A tooling strategy is maintained to support the business plan. Tool effectiveness is regularly reviewed. | Tool limitations are understood and mitigated with documented compensating controls and periodic assurance. |
